Breaking Down the Top 5 Java Security Vulnerabilities You Need to Patch ASAP
Discover the critical Java security vulnerabilities that demand immediate attention. Learn about…
Is Your Java Code Safe? Top 10 Vulnerabilities You Must Know
Discover the top 10 vulnerabilities that could jeopardize your Java code's security.…
Protecting Your Online World: 9 Special Roles of Message Digests in 2023
Explore the pivotal role of message digests in 2023 in safeguarding your…
How to unblock applications blocked by java security ? | 9 Secrets to Unblocking Java Security Applications
Java has been a cornerstone of software development for decades, advertising flexibility,…
A Beginner’s Guide to LDAP Injection | 10 Reasons to Consider an LDAP Injection
Within the world of cybersecurity, understanding vulnerabilities and potential dangers is basic…
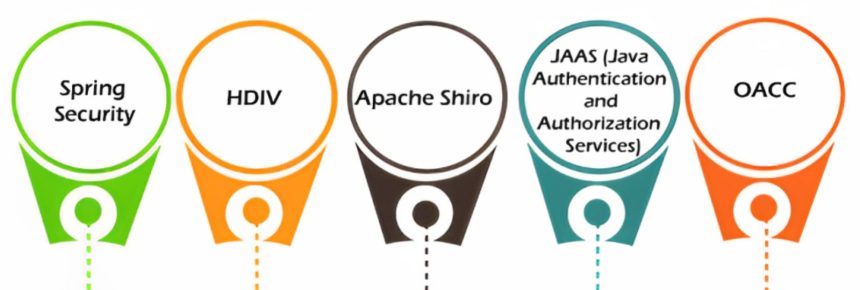
Thirteen rules for developing secure Java applications | Top Essential Elements for Developing Secure Java Applications-Techearth
ava, with its vigor and flexibility, has gotten to be a prevalent…
Java vs. Dot Net | 9 Tips for Making Java Safer Than Dot Net
Within the domain of software advancement, two noticeable programming stages, Java and…
Top 7 Facts About Java Security Issues | Why does Java have so many security issues?
Java, a broadly utilized programming dialect, has picked up notoriety due to…
Parameterization to Prevent Injection: A Comprehensive Overview | What Are the Best Practices for Avoiding Injection?
Infusion assaults pose a critical danger to the security of web applications.…
Java Web Security: | How to Understand the Different Things to Consider About Web Security
Web security is a pivotal aspect of creating and deploying Java-based web…